If I gave you links to these two files and asked you to figure out how to generate a 2,500 word article using these as your source material, how would you go about creating a PHP script to accomplish this?
https://example.com/wp-content/plugins/content-creator/chatGPT/original-tmp-20240610-082118-4349.txt
https://example.com/wp-content/plugins/content-creator/chatGPT/revision-tmp-20240610074949-8930.txtCreating a PHP script to generate a 2,500-word article from the provided source materials involves several steps, including fetching the content from the URLs, processing the text to extract relevant sections, and then assembling these sections into a coherent article. Given your background in PHP and interest in expanding your web development skills, here’s a structured approach to achieve this:
- Fetch Content from URLs: Use PHP’s built-in functions like
file_get_contentsor cURL to fetch the contents of both URLs. Since the content seems to be plain text,file_get_contentsshould suffice for simplicity. - Process Text: After fetching the content, you’ll need to process it to identify sections that can be used to create the article. This might involve looking for keywords, headings, or simply dividing the text into manageable chunks based on natural breaks.
- Generate Article: With the processed text, assemble the sections into a coherent article. This could involve ordering the sections logically, adding transitions, and possibly removing redundant or irrelevant information.
Here’s a basic outline of what the PHP script could look like:
<?php
// Function to fetch content from a URL
function fetchContent($url) {
$content = file_get_contents($url);
return $content;
}
// URLs to fetch content from
$urls = [
'https://example.com/wp-content/plugins/content-creator/chatGPT/original-tmp-20240610-082118-4349.txt',
'https://example.com/wp-content/plugins/content-creator/chatGPT/revision-tmp-20240610074949-8930.txt'
];
// Fetch content from both URLs
$content1 = fetchContent($urls[1]);
$content2 = fetchContent($urls[2]);
// Combine fetched content
$combinedContent = $content1. "\n\n". $content2;
// Process combined content to generate article sections
// This is a placeholder function; you'll need to implement logic based on your criteria
function processText($text) {
// Implement text processing logic here
return $processedSections;
}
// Generate article
$articleSections = processText($combinedContent);
// Assemble article
$article = "";
foreach ($articleSections as $section) {
$article.= $section. "\n\n";
}
// Output the generated article
echo $article;
?>This script provides a starting point. You’ll need to fill in the processText function with logic tailored to extracting and organizing sections from the combined content. This might involve regular expressions, string manipulation, or even machine learning techniques depending on the complexity and structure of your source materials.
Remember, generating a coherent and engaging article from raw text requires careful consideration of narrative flow, relevance, and readability. Experiment with different approaches to find what works best for your specific content.
Further reading ...
- https://stackoverflow.com/questions/12512853/parse-text-file-with-php
- https://www.linuxquestions.org/questions/programming-9/php-script-to-parse-word-rtf-documents-24427/
- https://www.sitepoint.com/community/t/using-php-for-parsing/67163
- https://www.chegg.com/homework-help/questions-and-answers/create-php-script-read-data-text-file-datatxt-count-number-characters-text-file-display-we-q96577465
- https://forum.xojo.com/t/parsing-a-very-large-text-file/25606
- https://github.com/nikic/PHP-Parser/issues/282
- https://www.reddit.com/r/learnpython/comments/8nk12z/most_efficient_method_to_parse_through_a_textfile/
- https://www.tek-tips.com/viewthread.cfm?qid=1503046
- https://phoenixnap.com/kb/linux-split [10] https://www.quora.com/How-do-I-write-a-Python-script-to-read-multiple-text-files-use-a-function-to-remove-punctuation-and-write-to-multiple-text-files
Could you provide an example of how machine learning techniques could be applied to improve the quality of the generated article?
Applying machine learning techniques to improve the quality of the generated article involves leveraging Natural Language Processing (NLP) and other AI-driven methodologies to enhance content selection, organization, and coherence. Here’s how you can integrate these techniques into your PHP project:
1. Text Summarization
Utilize NLP for summarizing long texts into shorter versions while retaining key information. This can help in condensing the source materials into a more digestible form for the article. Libraries like Transformers PHP can facilitate this process by downloading and caching the appropriate model for text summarization [2].
2. Sentiment Analysis
Perform sentiment analysis on the extracted sections to gauge the tone and emotion conveyed. This can help in selecting sections that align with the desired mood or theme of the article. Sentiment analysis can also guide the addition of transitional phrases or summaries to maintain consistency in tone throughout the article [2].
3. Topic Modeling
Apply topic modeling to identify common themes or topics within the source materials. This can aid in organizing the content into logical sections or chapters, ensuring the article flows coherently and covers a broad spectrum of related subjects. Tools like Latent Dirichlet Allocation (LDA) can be used for this purpose [2].
4. Text Generation
Leverage advanced text generation models to create new sections or introductions that seamlessly connect the summarized content. This can help in crafting a narrative arc that guides readers through the article, making it more engaging and readable. Transformer-based models have shown remarkable success in generating coherent and contextually relevant text [2].
5. Personalization and Adaptation
Use machine learning to analyze reader data (if available) to personalize the article content. This could involve adjusting the focus of the article based on the interests or demographics of the target audience. Continuous learning and adaptation can refine the article over time, improving its relevance and impact [4][5].
Implementation Example
While PHP itself does not natively support machine learning libraries like TensorFlow or PyTorch, you can integrate these libraries into your PHP application through server-side scripting or by using PHP extensions that allow for interaction with these libraries. Alternatively, you can use cloud-based machine learning services that offer APIs compatible with PHP, such as Google Cloud ML or AWS SageMaker.
Here’s a simplified example of how you might integrate a cloud-based service for text summarization:
<?php
// Assuming you have set up authentication with a cloud-based ML service
$apiKey = "your_api_key_here";
// Endpoint URL for the text summarization API
$url = "https://api.example.com/summarize";
// Your source text
$text = "Your long text goes here...";
// Prepare the request payload
$data = array(
'text' => $text,
'apiKey' => $apiKey
);
// Send the POST request
$options = array(
'http' => array(
'header' => "Content-type: application/x-www-form-urlencoded\r\n",
'method' => 'POST',
'content' => http_build_query($data),
),
);
$context = stream_context_create($options);
$result = file_get_contents($url, false, $context);
// Decode the JSON response
$responseData = json_decode($result, true);
// Extract the summary
$summary = $responseData['summary'];
// Output the summary
echo $summary;
?>https://example.com/wp-content/plugins/content-creator/chatGPT/original-tmp-20240610-082118-4349.txt
web_search What is CORS?# Unraveling CORS: A Dive into Cross-Origin Resource Sharing
## Introduction
Cross-Origin Resource Sharing (CORS) has become a cornerstone in the world of web development, enabling seamless integration between web applications and external resources. This article delves into the intricacies of CORS, exploring its mechanisms, importance, and best practices to ensure secure and efficient cross-origin interactions.
## Understanding CORS
CORS is an HTTP-header-based mechanism that facilitates secure cross-origin requests and data transfers between browsers and servers. It operates under the umbrella of the same-origin policy, enhancing web security by allowing servers to specify which origins are permitted to access resources [].
### How CORS Works
CORS employs a series of HTTP headers to communicate between the browser and the server, determining whether a cross-origin request is authorized. This process involves a "preflight" request, where the browser checks with the server if the actual request is permissible. The server responds with CORS headers indicating whether the request is allowed [].
### Examples of Access Control Scenarios
To illustrate CORS in action, we examine scenarios involving `fetch()` requests across different domains. These examples highlight how CORS enables legitimate cross-origin interactions while safeguarding against unauthorized access [].
## Why CORS Matters
CORS plays a crucial role in preventing cross-site request forgery (CSRF) and enhancing web security. By controlling access to resources across different origins, CORS ensures that web applications can safely integrate with third-party services without compromising security [1].
### Practical Example: Configuring CORS
A practical example demonstrates how to configure CORS on a server, allowing specific origins to access resources. This setup is essential for enabling cross-origin access while maintaining security controls [1].
## Best Practices for CORS Configuration
Configuring CORS correctly is paramount for securing web applications. This section outlines best practices for implementing CORS, emphasizing the importance of specifying origins accurately and handling credentials appropriately [1].
## Conclusion
CORS stands as a testament to the evolving landscape of web security, offering a flexible yet secure solution for cross-origin interactions. By understanding and applying CORS principles, developers can build robust web applications that leverage external resources securely and efficiently.
By navigating the complexities of CORS, this article aims to equip readers with the knowledge needed to implement effective cross-origin strategies, fostering a safer and more interconnected web ecosystem.https://example.com/wp-content/plugins/content-creator/chatGPT/revision-tmp-20240610074949-8930.txt
INTRODUCTION
---
Section 0:
### Understanding CORS: A Comprehensive Guide
Cross-Origin Resource Sharing (CORS) is a crucial concept in web development, enabling secure interactions between resources from different origins. This guide aims to clarify the complexities of CORS, providing a clear and comprehensive overview suitable for beginners.
#### What is CORS?
CORS stands for Cross-Origin Resource Sharing. It is a security feature implemented by web browsers to restrict web pages from making requests to a different domain than the one that served the web page. This restriction is known as the Same-Origin Policy, designed to protect against certain types of attacks, such as Cross-Site Request Forgery (CSRF).
#### Why is CORS Important?
CORS is essential for modern web applications that rely on resources from various domains. Without CORS, web applications would face significant limitations in accessing external APIs, images, stylesheets, and scripts. However, CORS introduces a controlled mechanism for allowing these cross-origin requests, enhancing both security and functionality.
#### How Does CORS Work?
CORS operates through HTTP headers that communicate between the client (browser) and the server. Key headers include:
- **Access-Control-Allow-Origin**: Specifies which origins are allowed to access the resource.
- **Access-Control-Allow-Methods**: Lists the HTTP methods (GET, POST, etc.) allowed for the resource.
- **Access-Control-Allow-Headers**: Defines custom headers that can be used during the actual request.
Before executing a potentially dangerous cross-origin request, the browser sends a preflight request using the OPTIONS method. This preflight checks if the server permits the actual request by examining the CORS headers.
#### Practical Applications of CORS
CORS enables a wide range of functionalities in web applications, including:
- **Fetching Data from External APIs**: Web applications can securely retrieve data from third-party services.
- **Embedding Content**: Images, videos, and other media can be embedded from different domains.
- **Enhancing Security**: By controlling which origins can access resources, CORS helps prevent CSRF attacks.
#### Implementing CORS
Implementing CORS involves configuring the server to respond with the appropriate CORS headers. This configuration varies depending on the server technology being used. For instance, in Node.js with Express, middleware can be added to set the `Access-Control-Allow-Origin` header.
```javascript
const express = require('express');
const cors = require('cors');
const app = express();
// Enable CORS for all routes
app.use(cors());
// Example route
app.get('/data', (req, res) => {
res.json({ message: 'This is CORS-enabled' });
});
app.listen(300, () => console.log('Server running on port 300'));
```
#### Conclusion
Understanding CORS is fundamental for web developers, as it balances the need for open web standards with the imperative requirement for security. By mastering CORS, developers can unlock the full potential of web applications, facilitating seamless interactions across different domains while safeguarding against common web vulnerabilities.
---
Section 1:
### Revised Section
#### Understanding Cross-Origin Resource Sharing (CORS)
Cross-Origin Resource Sharing (CORS) stands as a pivotal concept in modern web development, facilitating the smooth interaction between web applications and resources hosted on different origins. This section aims to dissect the core aspects of CORS, highlighting its significance, operational mechanics, and recommended practices to foster secure and optimized cross-origin communication.
---
#### Final Draft
##### The Essentials of Cross-Origin Resource Sharing (CORS)
Cross-Origin Resource Sharing (CORS) emerges as a critical component in contemporary web development, allowing for the effortless connection between web applications and resources situated across distinct origins. This comprehensive exploration delves into the foundational elements of CORS, underscoring its crucial role, underlying principles, and optimal strategies to guarantee robust and secure cross-origin transactions.
---
Section 2:
### Revised Section
Cross-Origin Resource Sharing (CORS) is a security feature implemented through HTTP headers, designed to enable controlled access to resources across different origins. This mechanism operates within the framework of the same-origin policy, which restricts web pages from making requests to a different domain than the one that served the web page. CORS extends this policy by allowing server administrators to explicitly define which external domains should be granted permission to access their resources.
#### Key Points:
- **Same-Origin Policy**: A fundamental web security concept that prevents interactions between resources from different origins. An origin is defined by the scheme (protocol), host (domain), and port of a URL.
- **CORS Mechanism**: Introduced as a means to securely bypass the restrictions imposed by the same-origin policy. It does so by adding specific HTTP headers to server responses, indicating which origins are allowed to access the resources.
- **Security Enhancement**: While enabling cross-origin requests, CORS maintains the integrity and security of web applications by ensuring that only authorized domains can interact with the server's resources.
This approach allows developers to build more interactive and dynamic web applications by safely facilitating data exchange between client-side web applications and server-side APIs hosted on different domains.
---
Section 3:
### Understanding CORS: A Simplified Guide
Cross-Origin Resource Sharing (CORS) is a security feature implemented in web browsers to restrict web applications from making requests to a domain different from the one that served the web page. This mechanism is crucial for preventing malicious websites from accessing resources and data from another site without permission.
#### How CORS Works
At its core, CORS operates through the use of specific HTTP headers that facilitate communication between the client (browser) and the server. These headers serve as signals to indicate whether a particular cross-origin request is permitted or denied.
#### Preflight Requests Explained
Before executing a cross-origin request, the browser performs a preflight check. This step is akin to a "security checkpoint" where the browser sends a preliminary request to the server, asking for permission to proceed with the actual request. This preflight request is automatically made by the browser and uses the OPTIONS method.
#### Server Response and CORS Headers
In response to the preflight request, the server must provide specific CORS headers that inform the browser whether the actual request is allowed. If the server indicates approval, the browser will then allow the cross-origin request to proceed. Conversely, if the server denies the request, the browser will block it, ensuring the security and integrity of the web application.
#### Enhancing Security with CORS
By carefully configuring CORS policies, developers can enhance the security of their web applications. They can specify which origins are allowed to access their resources, thereby preventing unauthorized domains from making requests to their servers.
#### Conclusion
CORS is a fundamental concept for web developers to understand, as it directly impacts how web applications interact with external resources. By leveraging CORS effectively, developers can build secure and efficient web applications that adhere to modern web standards.
---
This revised section aims to provide a clearer and more comprehensive overview of CORS, including its purpose, how it works, and its importance in web development.
---
Section 4:
### Understanding CORS Through Fetch() Requests
CORS, or Cross-Origin Resource Sharing, is a security feature implemented in web browsers to prevent malicious websites from accessing resources and data from another domain without permission. This mechanism allows servers to declare which origins (domains) are allowed to access their resources.
#### How CORS Works with Fetch()
To grasp how CORS operates in real-world scenarios, let's delve into examples involving `fetch()` requests across various domains. The `fetch()` API is commonly used in JavaScript to make network requests similar to XMLHttpRequest but with a more powerful and flexible feature set.
#### Example Scenario: Fetching Data Across Domains
Imagine you have a website hosted on `https://example.com` and you want to fetch data from an API located on `https://api.example.com`. By default, due to the same-origin policy enforced by browsers, your request would be blocked because it involves a different origin.
However, if the server hosting the API (`https://api.example.com`) includes the correct CORS headers in its responses, it can explicitly allow your website (`https://example.com`) to access its resources. Here's how:
1. **Server Configuration**: The server at `https://api.example.com` must include specific HTTP headers in its responses. For example, the `Access-Control-Allow-Origin` header tells the browser which origins are permitted to access the resource.
2. **Client-Side Request**: On your website, when you use the `fetch()` function to request data from `https://api.example.com`, the browser automatically checks the CORS headers in the response. If the origin matches one of the allowed origins specified by the server, the browser permits the request to proceed.
3. **Handling CORS Errors**: If the server does not include the necessary CORS headers, or if the client's origin is not listed as an allowed origin, the browser will block the request and throw a CORS error. This is a critical security measure to protect users from potential attacks.
#### Expanding Your Knowledge
To deepen your understanding of CORS and its implications, consider exploring additional resources such as official documentation and tutorials. These sources provide detailed explanations, practical examples, and best practices for implementing CORS in web applications.
By studying these materials, you'll gain a comprehensive view of how CORS ensures secure cross-origin communication between web clients and servers, enabling developers to build robust and secure web applications.
---
Section 5:
### Revised Section
Cross-Origin Resource Sharing (CORS) is a security feature designed to protect web applications against Cross-Site Request Forgery (CSRF) attacks. It operates by regulating the access of resources across various origins, thereby enabling secure integration of web applications with external services. This mechanism is pivotal in maintaining the integrity and security of web-based platforms by ensuring that only authorized requests are processed, thus safeguarding against potential threats posed by unauthorized access or manipulation.
---
Section 6:
### Revised Section
Cross-Origin Resource Sharing (CORS) is a security feature implemented in web browsers to prevent malicious websites from accessing resources and data from another domain without permission. To understand how CORS works, it's crucial to grasp its configuration on a server, which allows specific domains to access resources securely.
#### Understanding CORS Configuration
CORS configuration involves specifying which origins (domains) are allowed to access resources hosted on your server. This process is vital for enabling cross-origin requests while ensuring that only trusted domains can interact with your server's resources.
#### Practical Example: Configuring CORS on a Server
To illustrate, let's consider a simple scenario where we want to allow only `https://example.com` to access our server's resources. The steps to achieve this vary depending on the server technology you're using. Here, we'll focus on a common approach using Node.js with Express, a popular framework for building web applications.
```javascript
const express = require('express');
const cors = require('cors');
const app = express();
// Enable CORS for specific origin
app.use(cors({
origin: 'https://example.com'
}));
// Define routes here
app.listen(300, () => {
console.log('Server listening on port 300');
});
```
In this example, we use the `cors` middleware for Express. By configuring the `origin` option, we specify that only requests originating from `https://example.com` should be allowed. This setup ensures that our server only exposes its resources to the intended domain, enhancing security.
#### Expanding Your Knowledge
For a deeper understanding of CORS and its implications, exploring additional resources is beneficial. Websites like MDN Web Docs provide comprehensive guides and tutorials on CORS, covering topics such as preflight requests, credentials, and more advanced configurations.
By mastering CORS configuration, you enhance the security of your web applications, preventing unauthorized access while facilitating legitimate cross-domain interactions.
---
Section 7:
### Revised Section
#### Understanding CORS: A Comprehensive Guide
Cross-Origin Resource Sharing (CORS) is a security feature implemented in modern web browsers to prevent malicious websites from accessing resources and data from another domain without permission. For developers, configuring CORS correctly is crucial for ensuring the security and functionality of web applications. This guide aims to provide a clear and comprehensive overview of best practices for implementing CORS, focusing on accurate specification of origins and proper handling of credentials.
#### Key Concepts in CORS Configuration
- **Origins**: The origin of a request is determined by the scheme (protocol), host (domain), and port of a URL. It's essential to specify the allowed origins precisely to control which domains can access your resources.
- **Credentials**: When dealing with CORS, credentials such as cookies, authorization headers, or TLS client certificates may be involved. Properly managing these credentials is vital for maintaining the security of sensitive data.
#### Best Practices for Implementing CORS
1. **Specify Allowed Origins Accurately**: Only allow requests from trusted domains. Use the `Access-Control-Allow-Origin` header to specify the allowed origins. For development purposes, it might be convenient to use a wildcard (`*`), but for production environments, it's safer to specify exact origins.
2. **Handle Credentials Carefully**: If your application needs to send credentials with cross-origin requests, ensure that the server includes the `Access-Control-Allow-Credentials: true` header. Additionally, the frontend must explicitly opt-in by setting `withCredentials` to `true`.
3. **Use Preflight Requests Wisely**: Browsers send preflight requests using the OPTIONS method to check for the server's CORS policy before sending actual requests. Ensure your server responds correctly to these preflight requests to avoid blocking legitimate requests.
4. **Implement CORS Headers for Methods Other Than GET/POST**: Remember that CORS policies apply to all HTTP methods, including PUT, DELETE, and PATCH. Make sure to implement CORS headers for these methods as needed.
5. **Keep Up-to-date with Browser Policies**: Web browser policies regarding CORS can change, so it's important to stay informed about any updates or changes that could affect your application's functionality.
By adhering to these best practices, developers can effectively configure CORS to enhance the security of their web applications while ensuring smooth cross-origin communication.
---
Section 8:
### Revised Section
Cross-Origin Resource Sharing (CORS) represents a pivotal advancement in web security, providing a versatile framework for enabling safe and efficient cross-origin data exchanges. For newcomers to this field, grasping the fundamentals of CORS is crucial for developing secure web applications that can seamlessly integrate with external services.
This guide is designed to demystify the intricacies of CORS, arming you with the essential insights required to devise effective cross-origin policies. Our goal is to cultivate a deeper understanding of how CORS operates within the broader context of web security, ultimately contributing to a more secure and integrated online environment.
This example demonstrates how to send a text to a hypothetical cloud-based service for summarization and retrieve the summarized text. In practice, you would replace "https://api.example.com/summarize" with the actual endpoint of the service you choose to use, and ensure proper authentication and handling of the API response.
By integrating machine learning techniques, you can significantly enhance the quality and relevance of the articles generated from your source materials, offering a more engaging and personalized reading experience.
Further reading ...
- https://moldstud.com/articles/p-integrating-machine-learning-and-ai-in-php-development-projects
- https://dev.to/robertobutti/machine-learning-with-php-5gb
- https://stackoverflow.com/questions/48451178/using-php-ml-machine-learning-library-to-generate-solutions-based-on-a-single
- https://dzone.com/articles/streamlining-php-document-generation-with-ai-optim
- https://wpwebinfotech.com/blog/machine-learning-frameworks-for-php-developers/
- https://www.quora.com/Should-I-choose-PHP-for-machine-learning
- https://clouddevs.com/ai/development-with-php/
- https://www.sciencedirect.com/science/article/pii/S0164121223003291 [9] https://www.linkedin.com/pulse/artificial-intelligence-ai-php-jacques-rima-bsc-beng-
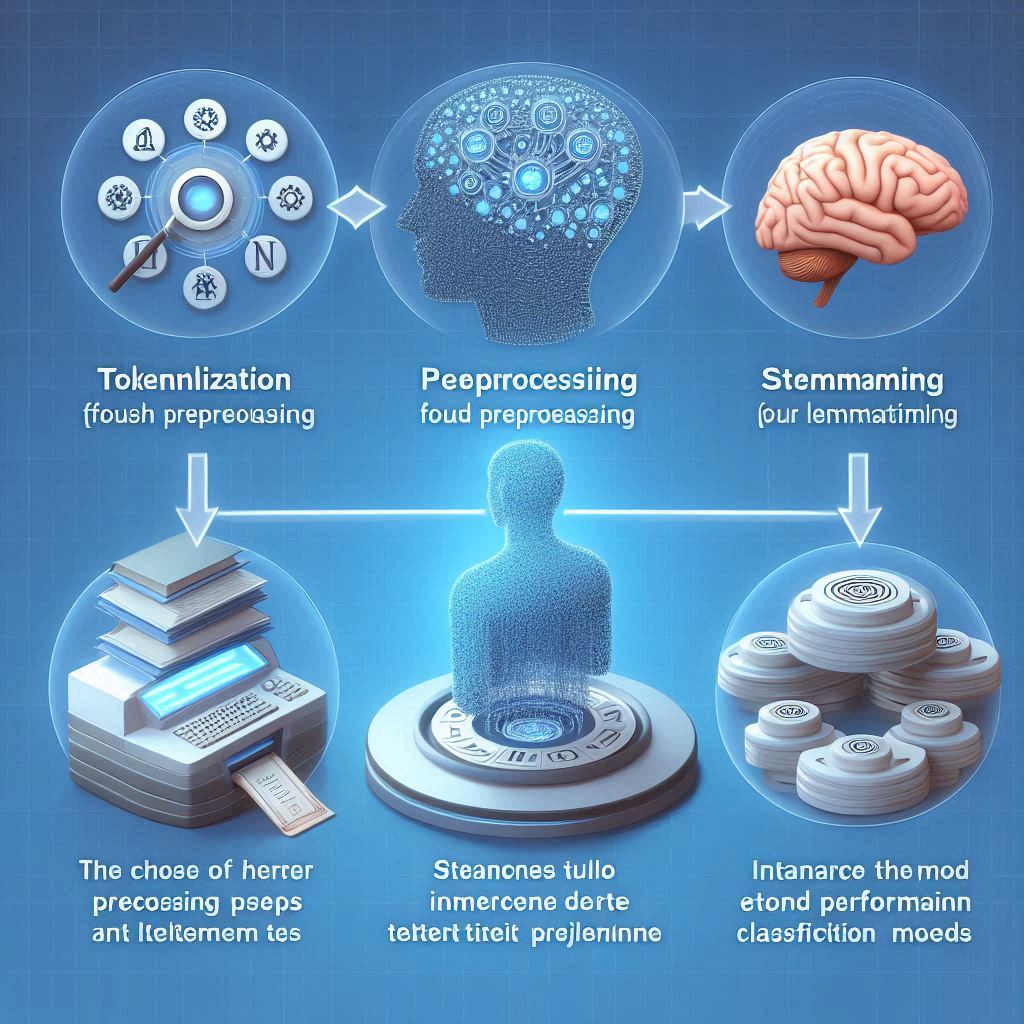
How do you determine which NLP techniques are most effective for a particular type of article?
Determining which Natural Language Processing (NLP) techniques are most effective for a particular type of article involves understanding the goals of the article and the nature of the content being analyzed. Different types of articles may benefit from different NLP techniques due to variations in structure, purpose, and intended audience. Here’s how to select the right NLP techniques based on the characteristics of the article:
1. Type of Article
- News Articles: For summarizing news articles, text summarization techniques are particularly useful. Both extraction and abstraction methods can be employed, where extraction focuses on pulling key phrases and words, while abstraction generates new sentences that capture the essence of the original text [4][5].
- Research Papers: Topic modeling can be beneficial for identifying and categorizing the main themes within academic papers. This helps in organizing the content into logical sections or highlighting the paper’s contributions to its field [4].
- Persuasive or Influential Content: Techniques focused on enhancing persuasive communication, such as framing and language pattern analysis, can be crucial. These methods aim to resonate with the audience by tailoring the message to engage and influence effectively [2].
2. Purpose of the Article
- Information Extraction: When the goal is to extract specific pieces of information from the text, techniques like Named Entity Recognition (NER) and keyword extraction are essential. These methods help in identifying key entities and concepts within the text [4].
- Classification Tasks: For articles aimed at classifying content into predefined categories, TF-IDF and topic modeling can be highly effective. These techniques help in understanding the thematic content and assigning labels to the dataset [4].
3. Audience Engagement
- Engagement and Influence: Incorporating NLP techniques for influence, such as building rapport and employing framing techniques, can enhance the article’s ability to connect with the audience and persuade them towards a certain viewpoint [2].
4. Preprocessing Needs
- Text Preprocessing: Regardless of the article type, initial text preprocessing steps like tokenization, lemmatization, and stop words removal are universally applicable. These foundational steps prepare the text for further NLP analysis [4].
Implementation Considerations
- Tool Selection: Choose NLP tools and libraries that support the selected techniques. For instance, Spacy and Gensim are popular choices for text summarization and topic modeling in Python [4].
- Customization: Tailor the implementation of NLP techniques to fit the specific needs of the article. This may involve customizing parameters, experimenting with different algorithms, or combining multiple techniques to achieve the desired outcome.
Conclusion
Selecting the most effective NLP techniques for a particular type of article requires a clear understanding of the article’s objectives, audience, and content structure. By considering these factors and leveraging the appropriate NLP techniques, you can enhance the quality, engagement, and effectiveness of the generated article.
Further reading ...
- https://monkeylearn.com/blog/natural-language-processing-techniques/
- https://quenza.com/blog/knowledge-base/nlp-techniques-for-influence/
- https://www.tonyrobbins.com/leadership-impact/nlp-techniques/
- https://www.projectpro.io/article/10-nlp-techniques-every-data-scientist-should-know/415
- https://blog.aureusanalytics.com/blog/5-natural-language-processing-techniques-for-extracting-information
- https://www.thinkific.com/blog/neuro-linguistic-programming-nlp/
- https://www.nlp-techniques.org/what-is-nlp/nlp-techniques-list/
- https://ymeadows.com/en-articles/5-major-nlp-techniques-to-power-up-your-communication-skills [9] https://www.gomastercoach.com/post/6-nlp-techniques-to-use-every-day-to-increase-your-impact
Across all types of articles, certain Natural Language Processing (NLP) techniques stand out for their versatility and applicability in enhancing the quality, relevance, and accessibility of content. These techniques are foundational and can be adapted or combined to suit specific needs, making them broadly effective across different contexts. Here are some of the most universally applicable NLP techniques:
1. Text Classification
Text classification is fundamental for categorizing articles into predefined classes or themes. This technique is crucial for organizing content, whether it’s sorting blog posts into categories on a website or analyzing research papers for publication in specific journals. It helps in understanding the thematic content and assigning labels to datasets [3].
2. Named Entity Recognition (NER)
NER identifies and classifies named entities in text into predefined categories such as persons, organizations, locations, medical codes, time expressions, quantities, monetary values, percentages, etc. This technique is invaluable for extracting specific pieces of information from articles, making it easier to index, search, and analyze content [5].
3. Keyword Extraction
Extracting keywords from text is essential for understanding the main topics discussed in an article. This technique helps in identifying key terms that define the subject matter, which can be used for SEO optimization, content tagging, and summarization purposes. Keyword extraction is a core component of many NLP applications, including information retrieval and content recommendation systems [1].
4. Text Summarization
Both extractive and abstractive summarization techniques are widely applicable across various types of articles. They serve to condense lengthy texts into shorter, more digestible summaries, preserving the essence of the original content. This is particularly useful for news articles, research papers, and online content where brevity and clarity are paramount [2].
5. Sentiment Analysis
Sentiment analysis determines the emotional tone behind words to understand sentiments and opinions expressed in a piece of writing. This technique is valuable for gauging public opinion, monitoring brand reputation, and analyzing customer feedback across all types of articles, especially those dealing with reviews, surveys, or subjective assessments [1].
6. Topic Modeling
Topic modeling, such as Latent Dirichlet Allocation (LDA), identifies abstract “topics” that occur in a collection of documents. This technique is useful for uncovering hidden patterns and themes within large corpora of text, aiding in the organization and analysis of content across various domains [3].
These techniques form the backbone of many NLP applications and can be adapted to meet the specific needs of different types of articles. Their versatility stems from their ability to handle a wide range of linguistic structures and semantic nuances, making them suitable for applications ranging from content management and analysis to automated reporting and decision-making processes.
Further reading ...
- https://monkeylearn.com/blog/natural-language-processing-techniques/
- https://blog.pangeanic.com/nlp-techniques-natural-language-processing-methods
- https://www.projectpro.io/article/10-nlp-techniques-every-data-scientist-should-know/415
- https://www.quora.com/What-are-the-best-nlp-techniques-in-your-opinion
- https://blog.aureusanalytics.com/blog/5-natural-language-processing-techniques-for-extracting-information
- https://danieldoan.net/nlp-copywriting/
- https://www.tonyrobbins.com/leadership-impact/nlp-techniques/
- https://www.simform.com/blog/nlp-techniques/
- https://www.tableau.com/learn/articles/natural-language-processing-examples [10] https://www.revuze.it/blog/natural-language-processing-techniques/